Overseas phone hackers broke into voice mailboxes at Texas A&M University on Jan. 9th and used the system as a springboard to make unauthorized collect calls, officials said.
“Initial indications look like we caught it pretty quickly,” Walt Magnussen, A&M’s telecommunications manager, said.
Of the university’s 25,000 phone lines, five voice mailboxes are known to have been infiltrated and used for fraudulent calls. The hackers were able to break in because each mailbox password was easy to guess – it was simply the phone number of that line, Magnussen said.
“It’s like using your name for your password,” he said. “It’s one of the first things people are going to guess.”
Soon after the hacking occurred, an emergency e-mail sent to employees instructed them to change their passwords to something secret if they had not already done so.
To prevent future fraudulent activity, the call-forwarding feature on university lines has since been disabled. A&M telecommunications supervisors also shut down other back doors that were being used to infiltrate the system.
Large businesses and universities are regularly targeted for such phone attacks because they have huge blocks of phone lines that make it easy for hackers to find a hole in security.
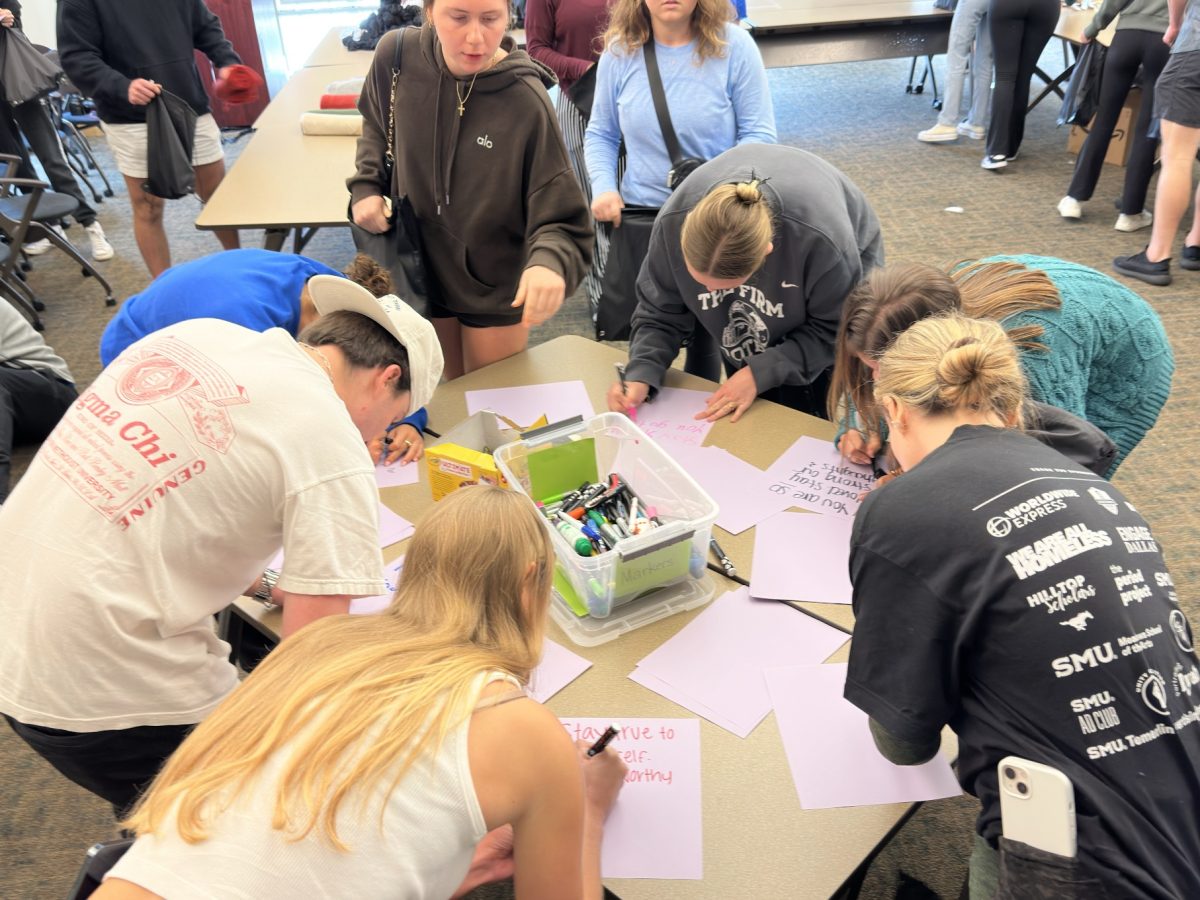
George Chrisman, associate vice president for Information Technology Services at SMU, advises students on campus to keep their password for anything very secret, and also to not write it down anywhere or share it with anyone. A combination of upper and lower case letters and numbers is suggested.
“The weakest link with anything is passwords,” Chrisman said.
Magnussen related the incident to security of another kind: “It’s similar to living in a house,” he said. “You can put all the locks you want on a door, but if you don’t use them, they’re useless.”
Convenience is a major factor, too. There are many features on phones that make operating the dorm phone system easier for students. However, when those features are abused, such as what happened with the hackers, precautions have to be taken.
“There is a trade out between security and convenience. I could very well put six locks on a door for extra protection, but it’s terribly inconvenient,” said Magnussen. “What we’re trying to do now is find that balance.”